Single Sign On (SSO)
Definitions
- Identity Provider (IdP) - This is your Identity Provider (Google, Okta, Azure AD).
- Service Provider (SP) - This is PagerTree.
SAML Required Attributes
- Version - 2.0
- Assertion Consumer URL (ACS) -
https://app.pagertree.com/public/saml/callback?sp_entity_id=<sp-entity-id> - NameIDPolicy - urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress
- Encryption - false
- Enable "advanced mode".
- Navigate to the Idp Configs page.
- Click New SSO Config button.
- In the new Idp Config form:
- Copy the metadata xml (or metadata url) from your IdP to the PagerTree
- Configure your IdP with the provided SP (PagerTree) information.
- Service Provider (PagerTree) Entity ID - Sometimes called the "audience" by the IdP.
- Service Provider (PagerTree) Assertion Consumer Service (ACS) URL
- Service Provider (PagerTree) Single Logout Service (SLO) URL
- Click Enable Button
Members of your account will now be required to sign-in using SSO via the Single Sign-On login page
Configuring PagerTree with SSO
-
Enable "advanced mode".
-
Navigate to the Idp Configs page.
-
Click New SSO Config button.
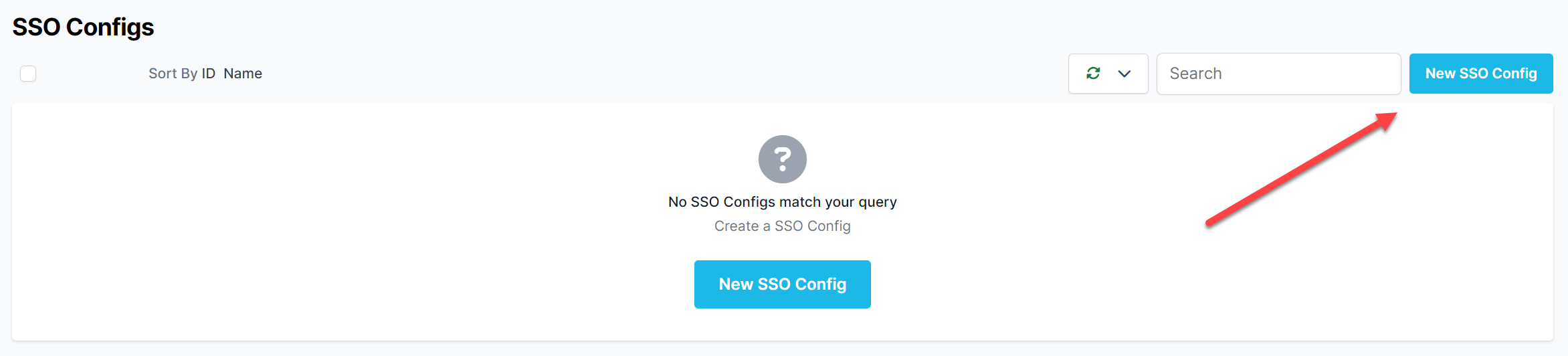
New SSO Config Button
-
In the new Idp Config form:
-
Copy the metadata xml (or metadata url) from your IdP to the PagerTree.
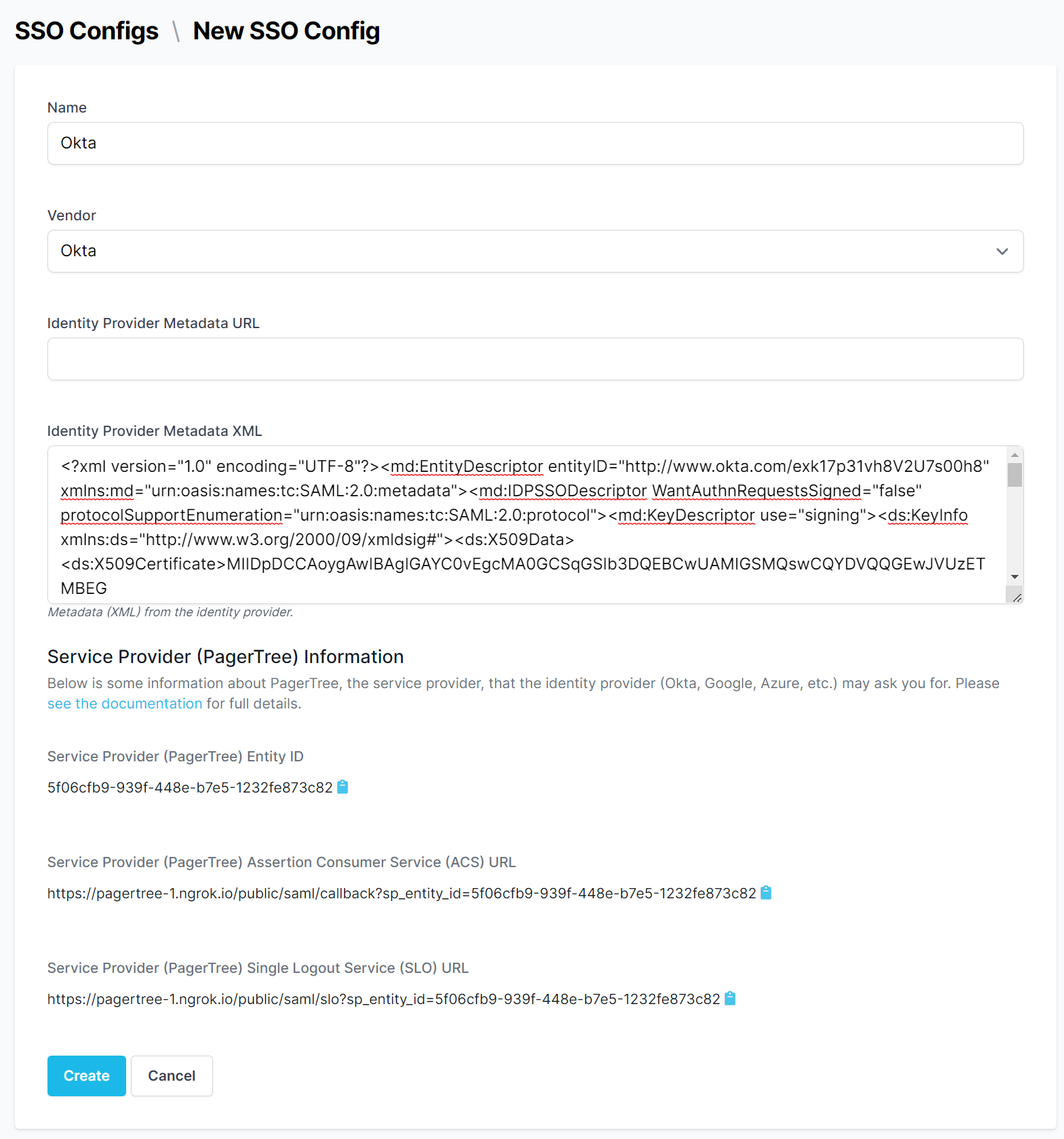
SSO Config Form
-
-
Configure your IdP with the provided SP (PagerTree) information.
-
Service Provider (PagerTree) Entity ID - Sometimes called the "audience" by the IdP.
-
Service Provider (PagerTree) Assertion Consumer Service (ACS) URL
-
Service Provider (PagerTree) Single Logout Service (SLO) URL
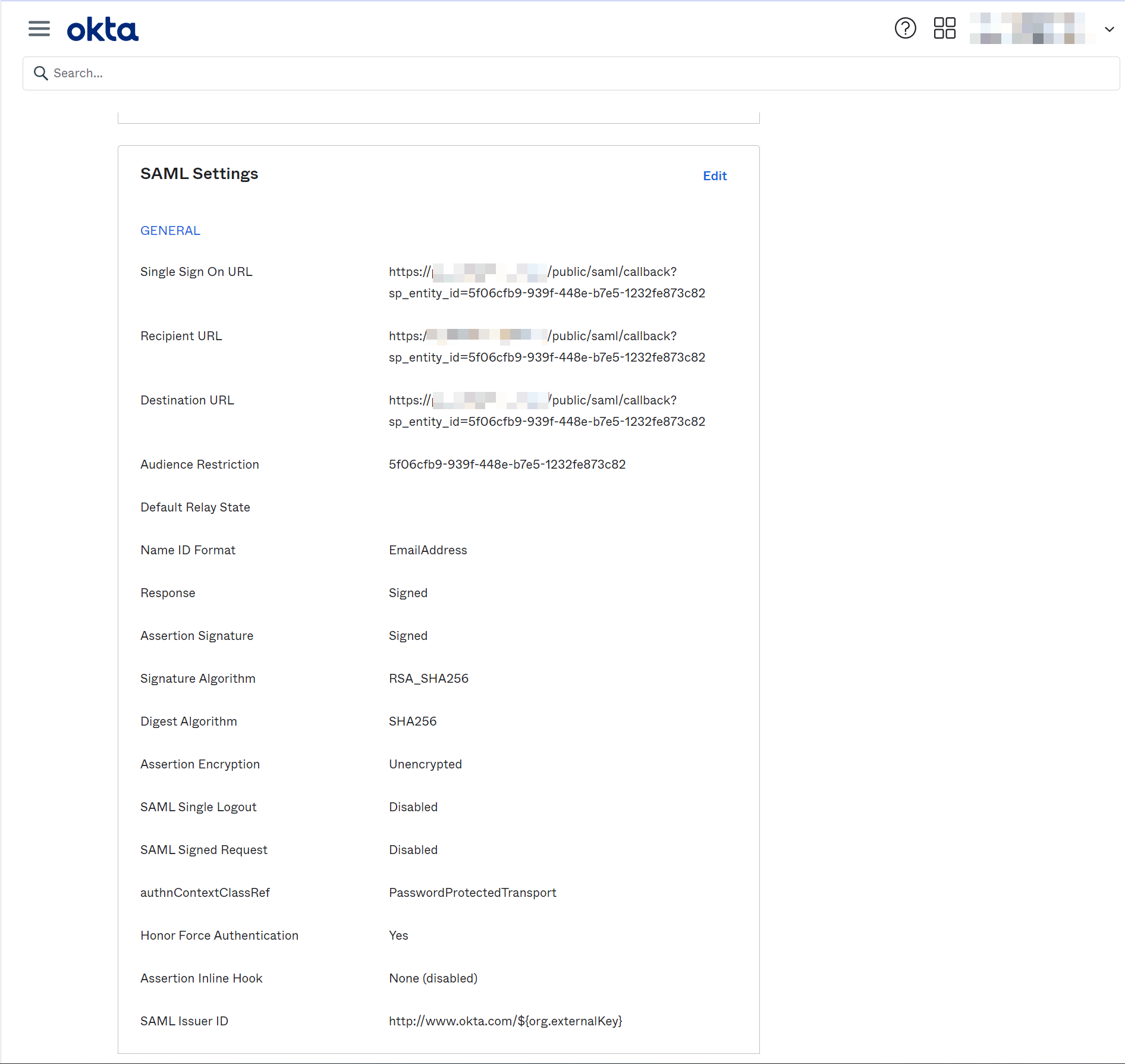
Identity Provider (IdP) Data
-
-
Click Enable Button.
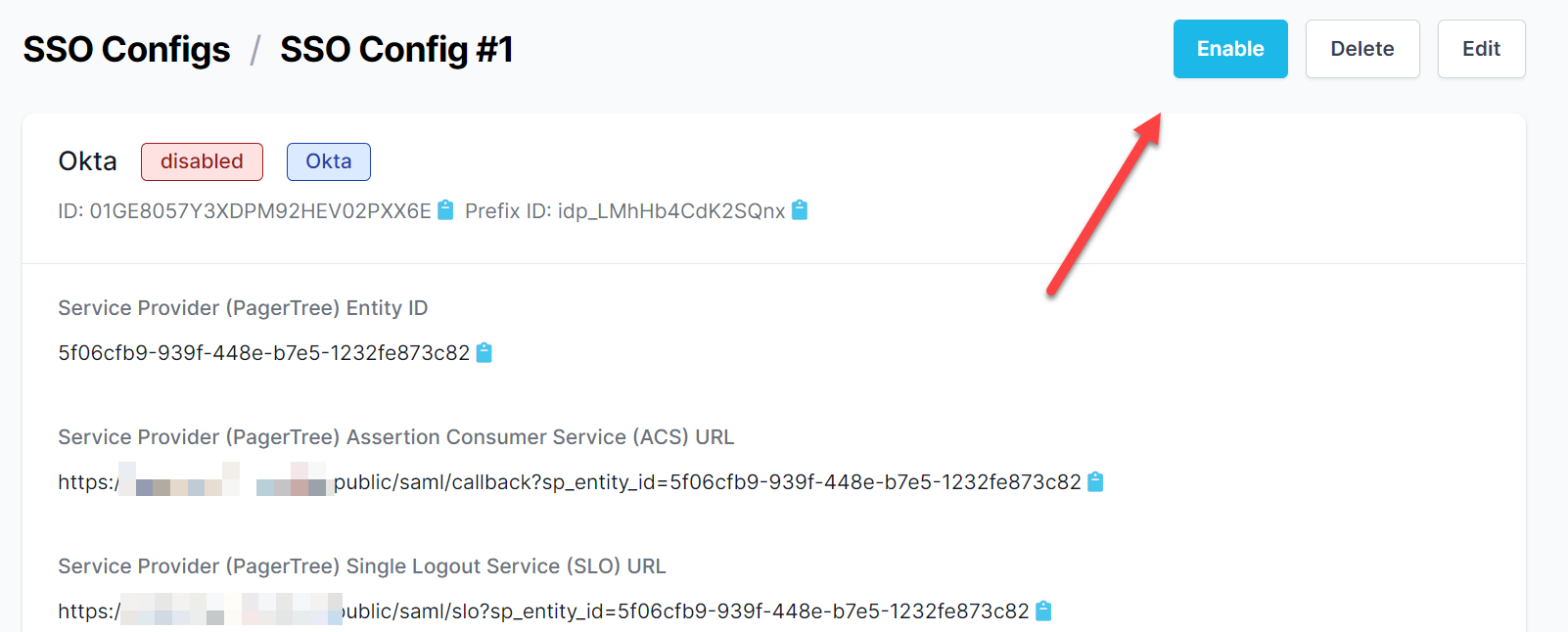
Enable SSO Config Button
Members of your account will now be required to sign-in using SSO via the Single Sign-On login page
Troubleshooting
Azure (Entra) Troubleshooting
Azure (Entra) users may encounter an "Invalid Idp Response: Invalid Audience" error due to Microsoft adding an extra "spn:" prefix to the Entity ID. To resolve this issue, switch your SSO Vendor type to Azure AD.
KeyCloak Troubleshooting
KeyCloak users may enounter a "null origin" error when trying to authenticate. To resolve this issue, adjust the following settings in KeyCloak:
- Set the "Force POST Binding" option to "ON" in the KeyCloak SAML client settings.
- Adjust the "Referrer Policy" (under Realm Settings > Security Defenses) to "strict-origin-when-cross-origin".
Authentik Troubleshooting
Authentik users need to ensure that the Authentik Vendor type is selected in the SSO Config form (PagerTree). Additionally, Authentik users need to select the Redirect option for the Service Provider Binding (in Authentik).